01Increased customer trust
When customers know that a company does software development professionally and implements measures to protect them, they’re more likely to do business with that company. This increased trust can also positively affect other aspects of the business relationship, such as contract negotiations or product evaluations.
02Improved reputation and branding
A good reputation is essential for any company, and having a strong security track record can be a major differentiator in today’s competitive software market. A company that has invested in security of its digital product or application can set itself apart from competitors and enjoy increased brand recognition.
03Increased sales and market share
Today’s software users are more aware of software security concerns, and they’re often willing to pay a premium for software that is known for its flawless security. A company that takes software security seriously can, therefore, enjoy increased sales and market share.
04Reduced software systems maintenance costs
Software that’s developed with security standards and best practices in mind from the start can reduce software maintenance costs by limiting the number of software issues. Fewer software bugs mean less software maintenance work.
05Reduced legal fees and expenses
Some of the software security issues can lead to lawsuits, including cases involving software patents, copyright infringement, and software licensing violations. Hiring or consulting a software development company that takes software security seriously can reduce the risk of legal fees or expenses.
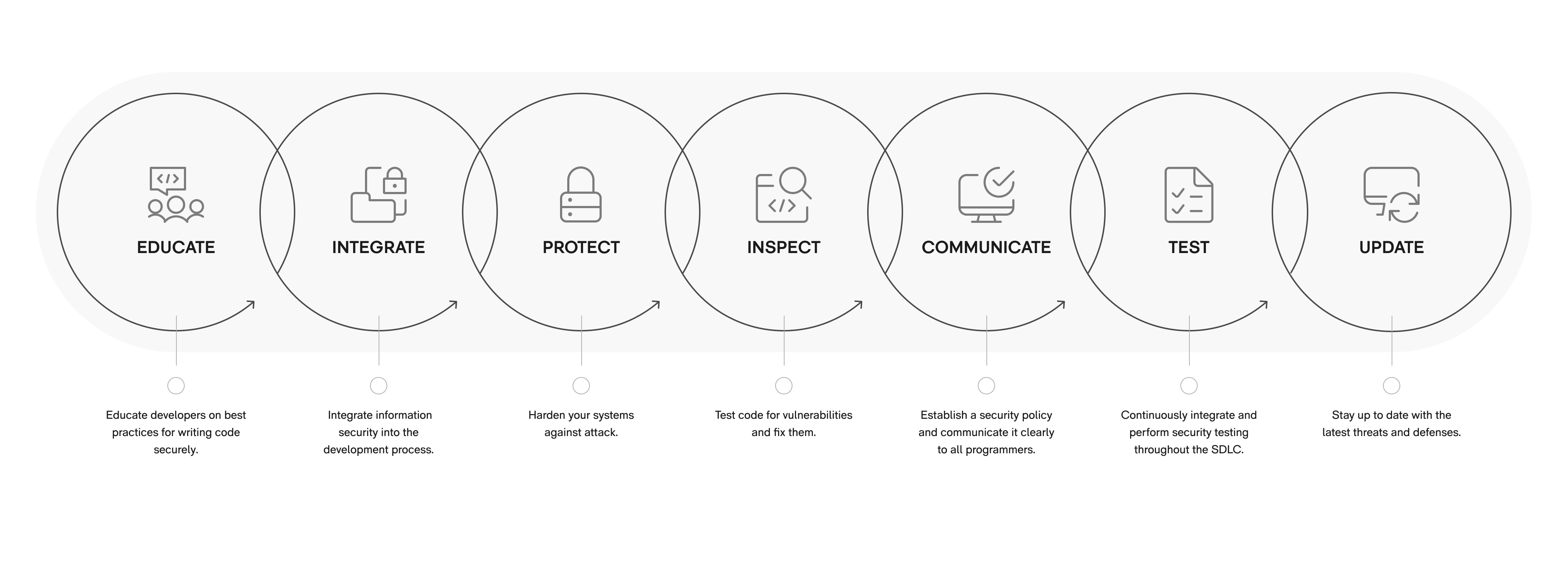
06Reduced software security testing costs
Many software security issues can be detected with security testing implemented throughout the entire development process. Security testing saves time and money when compared to software testing after the coding is complete.